(post describes my experience and does not represent my employer)
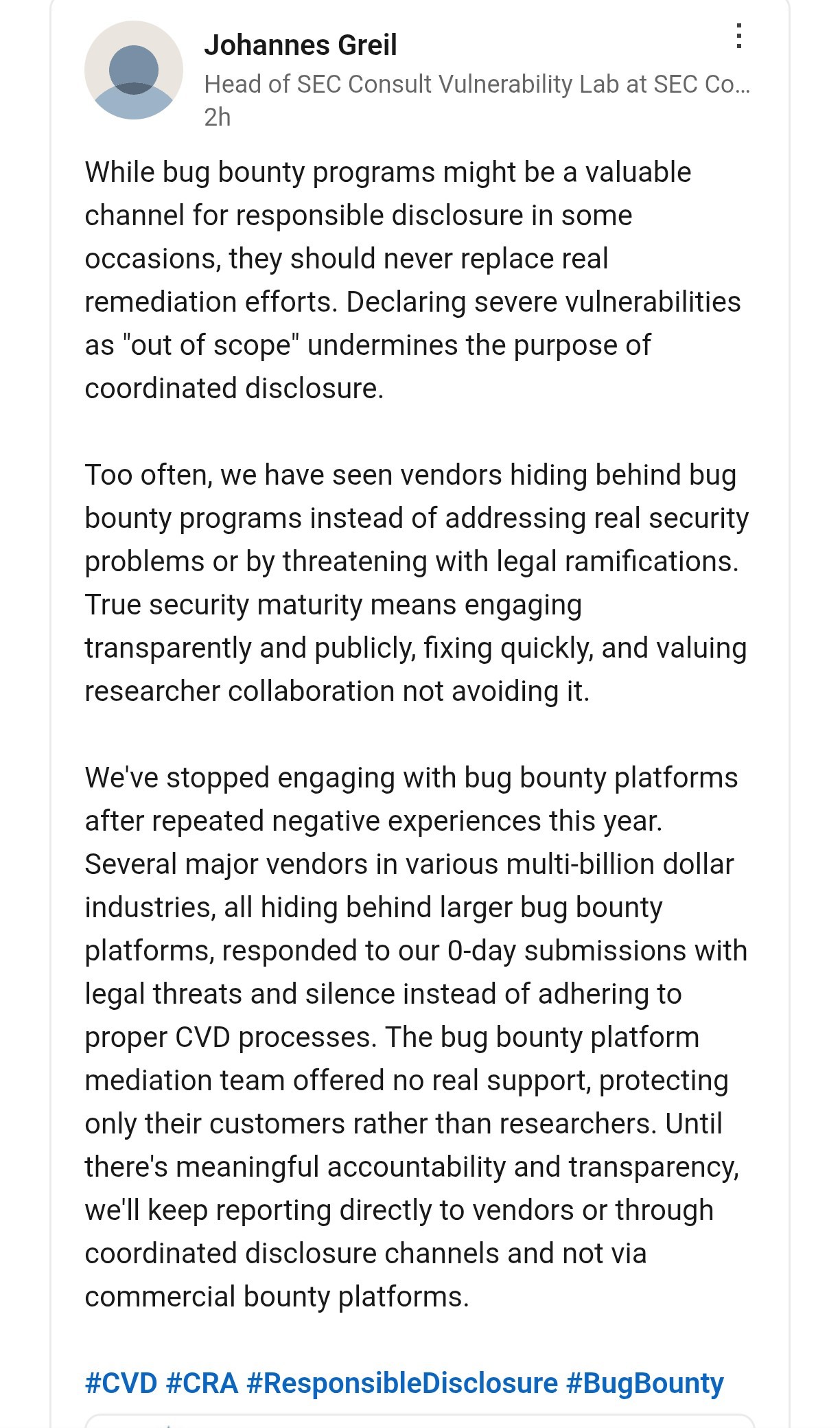
LinkedIn post (see also screenshot): https://www.linkedin.com/posts/johannes-greil-189bb813b_cybersecurity-infosec-workexaminer-activity-7386384177107116032-T3ow
I was involved in the mentioned cases and can only warn every penetration tester of bug bounty platforms.
I worked in an official CVE Numbering Authority (CNA) and we were legally threatened multiple times by vendors.
While bug bounty platforms claim to be a "safe harbor" and claim to mediate in difficult situations, in every instance they told us we have to adhere to the policies of the platform and didn't help any further. So, any user of these platforms has a double liability: first, to your country's law, second to the bug bounty platform's policy.
In the case of #HackerOne, they delegate this policy to the vendors:
"Security Teams will publish a program policy [...]. You should always carefully review this program policy prior to submission as they will supersede these [H1's] guidelines in the event of a conflict."
Source: https://www.hackerone.com/terms/disclosure-guidelines
So vendors can create a policy "no one is allowed to publish if we don't agree" and defeat responsible disclosure. In fact, some vendors do exactly that. Bug bounty platforms are paid by vendors and have no incentive to protect the researchers.
➡️ If you submit your vulnerability via email or similar directly to the vendor, then you are not legally bound to the bug bounty program's policy.
➡️ If there is trouble, involve your national CERT, they truly mediate.
Stay safe and warn your pentesting friends.