🚁 CVE-2026-32708 (HIGH): Stack-based buffer overflow in PX4-Autopilot (<1.17.0-rc2) via Zenoh uORB subscriber. Exploitable w/ local privileges; could crash or compromise drones. Upgrade ASAP. https://radar.offseq.com/threat/cve-2026-32708-cwe-121-stack-based-buffer-overflow-a8d143e4 #OffSeq #DroneSecurity #CVE #Infosec
When bombs fall, keyboards follow. The #Handala attack on #Stryker — 200,000 systems claimed wiped, 50TB stolen, timed explicitly to the US-Israeli assault on Iran — is textbook retaliation hacktivist logic. But here's the thing nobody wants to say out loud: it barely matters whether the group is genuinely aggrieved civilians or a state front wearing a keffiyeh. The effect is identical. The deniability is the point.
Governments have learned that a "spontaneous" hacktivist campaign does more reputational work than an official cyberunit ever could — and when the targeting is this clean, "spontaneous" deserves serious scare quotes. We saw it with pro-Russian groups after #Ukraine. We saw it with pro-Palestinian groups after #Gaza. We're seeing it again now with #Iran. The pattern is consistent enough to be a doctrine at this point.
What makes it strategically interesting — and analytically treacherous — is the deliberate ambiguity it manufactures. A group claiming to represent bombed civilians carries far more narrative weight than one that's transparently state-linked. Attribution becomes a second-order problem: even if the group is genuinely independent, states benefit from the chaos and quietly let it run. Sometimes they seed it. Sometimes they just watch. The outcome for the victim is the same either way.
The targeting logic follows a reliable playbook too. Not purely military or intelligence targets — those carry too much legal and escalatory risk. Instead: corporations with visible ties to the aggressor country, ideally ones with symbolic weight or defense adjacency. #Stryker, with its $450M U.S. military contract and the same name as an Army armored carrier, checked every box. The selection wasn't random. It was a message dressed as an attack.
For defenders, none of this is new — but the tempo is accelerating. Geopolitical flashpoints are now predictable threat amplifiers with a measurable lag between event and campaign. Your company's government contracts, your country of incorporation, your defense-adjacent partnerships — these are part of your attack surface whether you've modelled them that way or not. The groups carrying the flag may be real, fake, or somewhere in the uncomfortable middle. It doesn't matter. The wiper doesn't care about the ideology behind it.
→ Week #11/2026 also covers:
🇺🇸 FBI hacked,
🇨🇳 Salt Typhoon goes global,
🤯 🔓️ 💬 #Instagram dropping E2E encryption
🤖 ⏱️ An #AI agent hacked McKinsey's #chatbot in two hours.
Full issue 👉 https://infosec-mashup.santolaria.net/p/infosec-mashup-11-2026-when-bombs-fall-keyboards-follow
If you find it useful, subscribe to get it in your inbox every weekend 📨 #infosecMASHUP #cybersecurity #infosec #threatintel
🔥 CRITICAL: CVE-2026-26954 in SandboxJS (< 0.8.34) enables sandbox escape via Function & Object.fromEntries. Attackers can run arbitrary code remotely! Upgrade to v0.8.34+ now. Full details: https://radar.offseq.com/threat/cve-2026-26954-cwe-94-improper-control-of-generati-35790079 #OffSeq #CVE202626954 #infosec #sandbox
⚠️ CRITICAL: CVE-2026-32746 in GNU inetutils telnetd (<=2.7) enables remote buffer overflow — unauthenticated code execution or DoS possible. Disable telnet, restrict access, monitor for threats. No patch yet! https://radar.offseq.com/threat/cve-2026-32746-cwe-120-buffer-copy-without-checkin-0ceead78 #OffSeq #CVE202632746 #infosec
🚨 CRITICAL: CVE-2026-32626 in AnythingLLM Desktop ≤1.11.1 lets attackers run code via XSS → RCE (CVSS 9.7). No patch yet. Restrict chat, harden Electron, sanitize input. High risk, act now! More: https://radar.offseq.com/threat/cve-2026-32626-cwe-79-improper-neutralization-of-i-a50f3d86 #OffSeq #XSS #RCE #InfoSec
RE: https://hachyderm.io/@evacide/116223380207438934
"The development comes days after #TikTok said it does not plan to introduce #E2EE to secure direct messages on the platform, telling BBC News that the technology makes users less safe and that it wants to protect users, especially young people, from harm."
Aka "But think about the children!!!111one"
Instagram is getting rid of end-to-end encrypted messages after May 8, 2026, arguing that people barely used the feature, which is not enabled by default and only available in some areas. Here's more from @Engadget.
ASN: AS4837
Location: Tianjin, CN
Added: 2026-03-06T06:02
Welcome to 🌙 Shark after Dark 🌙
This account features less-than-stellar and likely reality-detached toots, e.g. infosec meta-commentary, technology rants, life quibbles, w/e.
It serves as an (experimental) alt account for @shellsharks as part of my "social horcrux" lifestyle. If you follow me over there, this account should be familiar, albeit slightly more unhinged.
So if you want a li'l more Shellsharks in your feed, sub away! 🦈 🦈
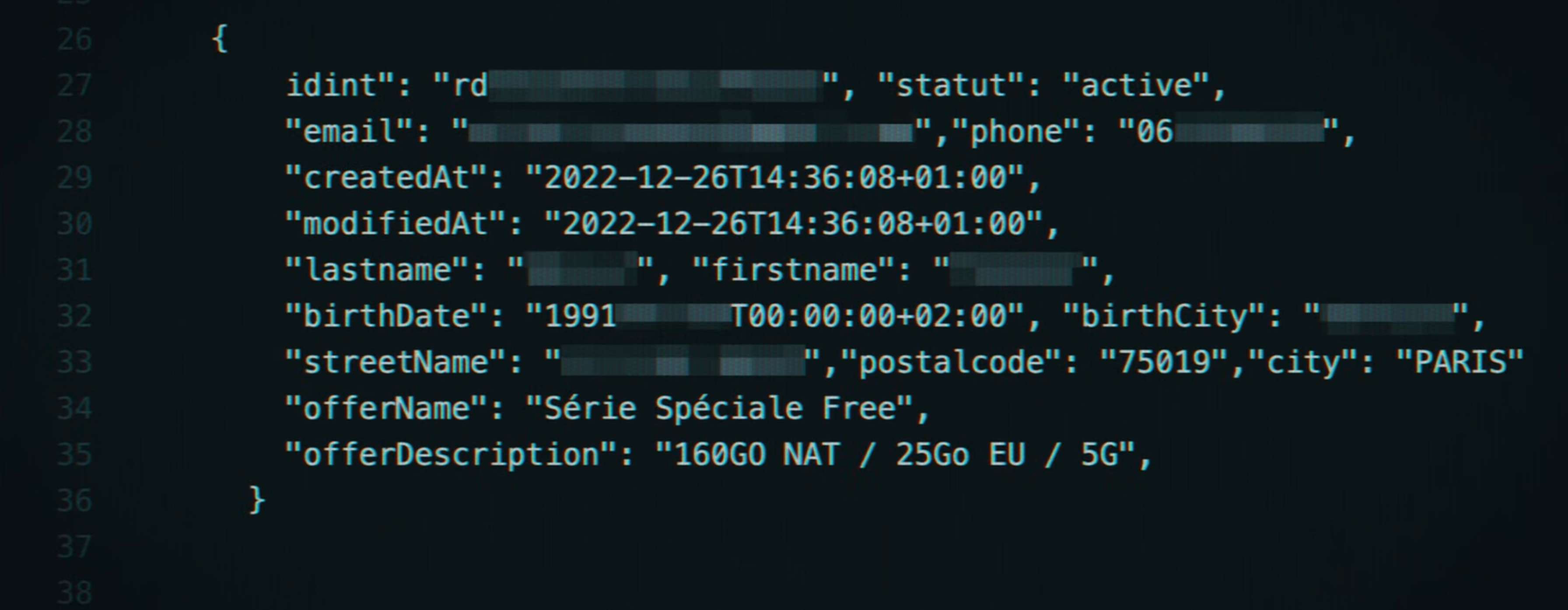
La fuite de données de Free a permis à Ludoc de retrouver un preneur d’otage disparu depuis 2018. Tu n’as pas “rien à cacher” sur internet.
Le dernier épisode de Sous Influence, le documentaire du réalisateur Ludoc, cherche à localiser un homme atteint de schizophrénie et hospitalisé.
⭐ Announcing a Major Architectural Update to RIFT ⭐
RIFT has undergone a complete rearchitecture to enhance its modularity, extensibility, and usability. An experimental build has been released on our GitHub repository, while the stable build remains available. The experimental build will continue to receive updates and improvements over time.
❓ What is RIFT?
RIFT is a valuable tool for reverse engineers, designed to generate on-demand FLIRT signatures for Rust binaries.
❗ What's new?
⚙️ Three Operation Modes:
- File Analysis Mode: Point RIFT directly at a binary.
- Direct Generation Mode: Target specific crate versions and compiler combinations.
- HTTP API Server Mode: Run RIFT as a service with an async job queue.
🔧 Modernized Ida Pro Plugin: The Ida Plugin has been rebuilt with server integration, enabling FLIRT signature generation while reversing without needing to leave the window.
For more details, visit: https://github.com/microsoft/RIFT
#reverseengineering #malware #rift #infosec #opensource #binaryanalysis
Join OWASP Global AppSec EU 2026 in Vienna, June 22–26, for hands-on training, epic talks, and networking with the best community vibes! 🚀
Secure your spot 👉 https://owasp.glueup.com/event/owasp-global-appsec-eu-2026-vienna-austria-162243/home.html
Is this the first time a major service has removed end-to-end encryption instead of adding it? Why Instagram?
#instagram #socialmedia #privacy #infosec #technology #enshittification
KB4830: Vulnerabilities Resolved in Veeam Backup & Replication 12.3.2.4465
#vulnerability #infosec #cybersecurity
🔗 https://vulnerability.circl.lu/bundle/08c1bcc5-abc2-4fd7-8a14-32dffe5c9afc
🔙 🚪 Researchers found a new backdoor called #Slopoly, likely generated with #AI, used in an Interlock ransomware attack to steal data.
Slopoly is a simple #PowerShell client that beacons to a C2 server, runs commands, and keeps persistence.
#IBM X-Force links the attack to a financially motivated group known as Hive0163 and says AI tools are speeding custom malware development.
#infosec #cybersecurity #tech #ibmxforce #xforce #threatintel
https://www.ibm.com/think/x-force/slopoly-start-ai-enhanced-ransomware-attacks
We are delighted to announce that GitGuardian will be joining us as a Silver sponsor for the first time this year.
🤝 Special thanks to the local team: Maxime Moroté & Jérémy Lanfranchi.
👉 Book your seat now and be part of the community: https://insomnihack.ch/?utm_source=mastodon&utm_medium=image&utm_campaign=Insomnihack2026&utm_content=1303
#InsomniHack #Cybersecurity #Infosec #INSO26 #CyberConference
Local privilege escalation bug in AppArmor. Update your Ubuntu and Debian systems and reboot.
🚨 CRITICAL: CVE-2026-32248 in parse-server (>=9.0.0, <9.6.0-alpha.12, <8.6.38) allows unauth attackers to hijack accounts if anonymous auth is enabled. MongoDB & PostgreSQL affected. Upgrade ASAP or disable anonymous auth! https://radar.offseq.com/threat/cve-2026-32248-cwe-943-improper-neutralization-of--cc26229b #OffSeq #CVE202632248 #infosec
⚠️ CRITICAL: CVE-2026-32251 in tolgee-platform (<3.166.3) allows authenticated users to exploit XXE for file read & SSRF. Patch to 3.166.3+ ASAP! Limit XML imports & monitor for abuse. Details: https://radar.offseq.com/threat/cve-2026-32251-cwe-611-improper-restriction-of-xml-6ee364da #OffSeq #CVE202632251 #infosec #XXE
🔴 CRITICAL: CVE-2026-32304 in locutusjs (<3.0.14) enables unauthenticated remote code execution via create_function() and unsanitized inputs. Patch to 3.0.14+ now! Full details: https://radar.offseq.com/threat/cve-2026-32304-cwe-94-improper-control-of-generati-7207fd62 #OffSeq #Vuln #JavaScript #Infosec
There’s a vulnerability with Proton VPN on macOS. The kill switch leaks your real IP between connections.
Glad I keep my router updated! My logs going back to Dec 31 don't have any matching IP addresses.
The honeymoon phase of AI-driven productivity is meeting the harsh reality of system stability. Amazon has officially updated its internal policies to require senior engineers to sign-off for any code changes assisted by generative AI. This move follows a series of significant service disruptions—referred to internally as "high blast radius" incidents—where AI-generated code led to major product outages.
For a company that values speed and a "you build it, you run it" culture, this is a massive shift. It turns out that while AI can write code in seconds, the cost of an error at AWS scale can be measured in hours of downtime and millions in lost revenue. We are seeing a necessary correction: AI is a powerful assistant, but it cannot yet be trusted with the keys to the kingdom without a seasoned human expert verifying the logic.
🧠 Amazon now mandates senior review for all AI-assisted code deployments.
⚡ The policy change follows a spike in high-priority Sev2 incidents.
🎓 Senior engineers must now act as the ultimate "bar raisers" for synthetic code.
🔍 This internal friction highlights the hidden costs of AI-driven development.
https://arstechnica.com/ai/2026/03/after-outages-amazon-to-make-senior-engineers-sign-off-on-ai-assisted-changes/
#EngineeringManagement #CloudComputing #GenerativeAI #security #privacy #cloud #infosec #cybersecurity
The line between national security and political surveillance is thinning. Congressional Democrats just launched an inquiry into the Department of Homeland Security regarding its use of administrative subpoenas. Unlike the subpoenas you see in courtroom dramas, these do not require a judge’s signature. They allow federal agencies to demand personal information and internal communications directly from technology companies with almost zero outside oversight.
This investigation follows reports that DHS used these "judge-free" demands to gather data on Americans who criticized the agency on social media. It is a significant moment for anyone in the tech industry. When the government can compel your data without a warrant, the First Amendment starts to look very fragile. You should watch how these tech firms respond to the inquiry, as it will set the standard for how they protect your information from administrative overreach.
🧠 Lawmakers are demanding to know how often DHS uses subpoenas without judicial review.
⚡ The inquiry follows evidence that critics of agency policy were specifically targeted.
🎓 Major tech platforms must now disclose their internal protocols for handling these federal demands.
🔍 Civil liberties groups are pushing for new legislation to require a judge’s approval for all data seizures.
https://www.washingtonpost.com/nation/2026/03/02/subpoenas-free-speech-congress-investigation/
#DataPrivacy #DigitalRights #TechLaw #security #privacy #cloud #infosec #cybersecurity